×Close
Forgot Your Password Message:
Close
×Close
Close
ATM Fraud , Endpoint Security , Fraud
'Cash Out' Malware Attackers Increasingly Infect ATMs From Afar, Experts Warn Photo: Europol, Trend Micro
Photo: Europol, Trend MicroAttackers are increasingly hacking into banks' networks to gain access to the IT infrastructure connected to their ATMs, security experts warn. Attackers then push malware onto the ATMs that allows a low-level gang member to walk up and enter a preset numerical sequence into the ATM to make it dispense all of its money in what's known as a "jackpotting" or "cashing out" attack.
See Also: Ransomware: The Look at Future Trends
Such attacks also enable criminals to steal credit and debit card data from ATM machines.
For attackers, the appeal is simple: Compared to walking into a bank with a gun and attempting to rob it, it's safer - and easier - to remotely infect an ATM, then dispatch low-level gang members, known as money mules, to physically walk away with cash from infected ATMs.
So far, however, these types of attacks have yet to be unleashed in many larger regions, such as the United States and Canada. That's according to EC3 - the European Cybercrime Center, part of the EU's law enforcement intelligence agency, Europol - and Tokyo-based security firm Trend Micro, which have issued a joint report into what they say have been "a seeming spate of remotely orchestrated attacks" designed to infect ATMs with malware from afar.
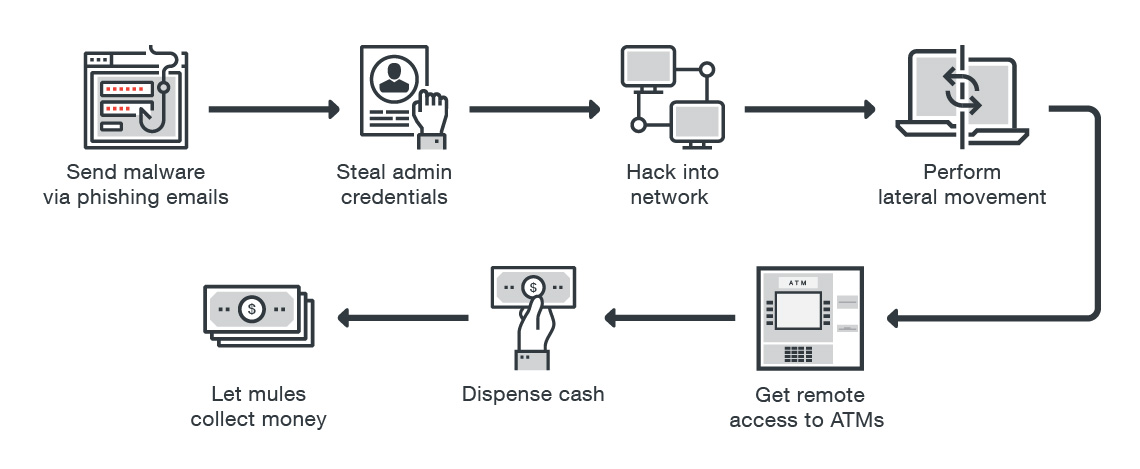 Many remote attacks that install malware on ATMs begin with a phishing attack against a bank employee. (Source: Europol and Trend Micro)
Many remote attacks that install malware on ATMs begin with a phishing attack against a bank employee. (Source: Europol and Trend Micro)"While network-based attacks require more work than do physical attacks, their appeal lies in allowing cybercriminals to extract cash on command without having to seek out the targeted ATMs," according to a Tuesday blog post published by Trend Micro security researchers. They warn that these remote-access attacks can also bypass existing defenses, such as any firewalls, VPNs or network segmentation that might be in place.
One such campaign targeted 41 ATMs in Taiwan in July 2016, resulting in the theft of $2.7 million in cash. Police said attackers installed malware on 22 ATMs manufactured by Wincor-Nixdorf - now known as Diebold Nixdorf - run by the country's First Commercial Bank after first hacking into the bank's London-based networks. According to Taiwanese consultancy iThome - as cited in the Europol and Trend Micro report - the hackers then "accessed the bank's voice recording system and stole the domain administrator's account credentials," used the credentials to gain VPN access to the bank's Taiwan branch, mapped the company's intranet topology, identified the ATM software updating system and figured out the required administrator credentials.
From there, "attackers logged into the ATM update server and set up a fake update package to the distribution management system," according to the report. "They then uploaded it to the ATMs as if it were a real update." The package instructed the ATMs to enable their telnet service, which the attackers used to remotely access the ATMs and upload three pieces of malware, including a test program that money mules, standing in front of an ATM, validated had been successfully executed.
"The mules in front of the machines reported the test results back to the remote hackers by using the Wickr Me secure messenger app on their mobile phones," according to the report. "Once the hackers confirmed that the ATMs were ready for the attack, they uploaded and ran modified vendor test tools that dispensed 40 banknotes at a time" - the maximum that the machine could dispense at once.
The money mules then moved to another ATM and repeated the process, according to the report. "In the meantime, the remote hackers wiped the malicious programs off the victimized ATM and logged off."
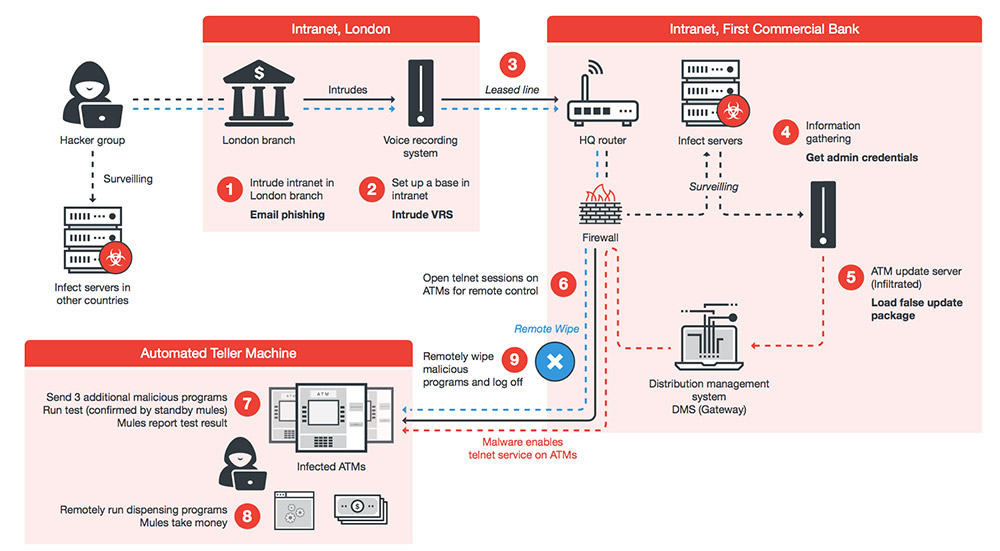 Taiwan network attack. (Source: Europol and Trend Micro)
Taiwan network attack. (Source: Europol and Trend Micro)Meanwhile, in July and August of last year, a cybercrime gang hacked into Thailand's Government Savings Bank's network to install new Ripper malware onto NCR-built ATMs managed by the bank. Subsequently, three groups of men jackpotted 21 ATMs across six provinces in Thailand, making off with a total of 12 million baht ($363,000) in cash, police say.
The Ripper campaign, which came to light before the attacks in Taiwan, was the first known attack that involved installing jackpotting malware onto ATMs without having to physically access the ATMs to do so, according to Europol and Trend Micro.
Instead, security researchers say these attacks most likely begin with spear-phishing emails carrying malicious executable files - malware - as attachments, which the gang sends to prescreened lists of bank employees. If victims fall for this social engineering attack, the malware gives attackers a beachhead on the victim's PC that they use to attempt to move laterally through the bank's network, access the ATM infrastructure and then infect as many ATMs as possible.
In the case of the Ripper attacks against the Thai bank, for example, NCR said that after breaching the bank's network, the attackers spoofed "the software distribution server as the means to deliver the malware to ATMs."
Banks may be unaware they've been hacked until money goes missing. Some types of malware are also designed to delete themselves from an ATM after they've been used to jackpot it, "effectively dissolving most traces of the criminal activity," according to Trend Micro.
Attacks have also been seen in other regions. As of September 2016, for example, Moscow-based security firm Group-IB says that cybercrime gangs using Cobalt ATM jackpotting malware had struck banks in Russia, the United Kingdom, the Netherlands, Spain, Romania, Belarus, Poland, Estonia, Bulgaria, Georgia, Moldova, Kyrgyzstan, Armenia and Malaysia, stealing an estimated $25 million.
Malware known as Carbanak - aka Anunak - has also been tied to thefts of more than $1 billion, although that figure is a mix of fraudulent wire transfers, using banking Trojans installed on PCs, as well as attacks that implanted malware on ATMs in person, according to Moscow-based security firm Kaspersky Lab.
Europol and Trend Micro say that while there are "striking similarities" between the Carbanak and Cobalt attacks, it's not clear if they're the work of the same group.
While there's been a growth in remote ATM attacks as well as other types of "logical" attacks that involve malware, physical attacks remain the most common type of attack vector against ATMs.
 Source: Europol and Trend Micro
Source: Europol and Trend MicroThe European Association for Secure Transactions, based in Edinburgh, Scotland, reports that the number of thefts that resulted from physical attacks against ATMs in Europe rose by 12 percent from 2015 to 2016. In particular, explosive attacks - including explosive gas and solid explosive attacks - increased by nearly 50 percent, to 1,000 such incidents in 2016. EAST says losses attributed to physical attacks in 2016, unchanged from recent years prior, was about €49 million ($57.5 million).
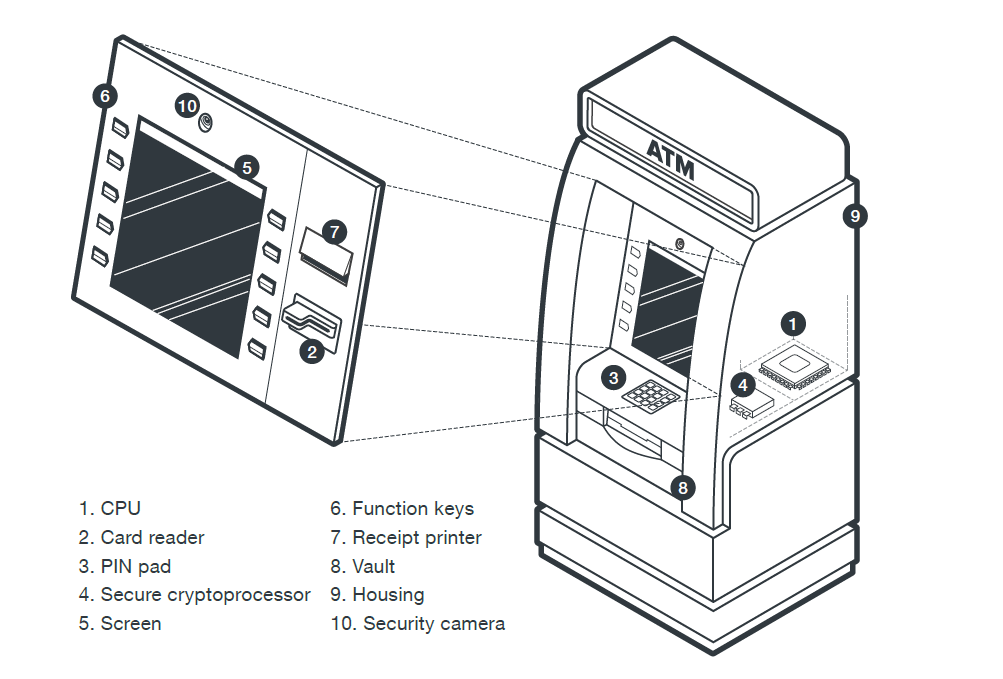
Here are some popular, old-school ways to steal cash from an ATM:
Ports: Crack open the ATM case and load jackpotting malware via USB or CD-ROM, or another access port. Sometimes gangs will use two teams - one installs the malware, while another waits to jackpot numerous infected ATMs in one fell swoop, often overnight or during a weekend. Black box: Physically access the ATM and plug in a purpose-built black-box to override security controls, then proceed as above. Skimmer: Install a skimmer glued into the mouth of the card reader - or in the form of a fake PIN pad, glued over the real one - that can read and store the data stored on cards' magnetic stripes, as consumers feed their cards into machines, and in some cases broadcast the data to a waiting attacker via Bluetooth. Ram raid: Ram the ATM or its enclosure using a vehicle, then attack the ATM with hammers or other tools to steal the cash it stores. Robbery: Rob an ATM technician who comes to service or refill the device. Explosives: If all else fails, open the ATM shutter and pump it full of explosive gas, then light a fuse and run until it potentially rains paper notes.It's the age of "open banking," and that means changes for banking institutions and their customers - as well as for the fraudsters. Shaked Vax of IBM Security Trusteer talks about new vulnerabilities and anti-fraud strategies.
Vax, the Identity and Anti-Fraud Solutions Strategist at IBM Security Trusteer, says the modern app era of open banking has completely transformed banking and customers' expectations.
"Users expect banks to develop innovative technology to not only meet their needs, but to provide a more secure banking experience and financial services," Vax says. "Banks are now faced with increased competition from FinTechs, demand for innovation to compete with the FinTechs, and delivering a seamless customer experience as much as possible."
The problem is: just as the open banking era makes business easier for customers, it also enables new opportunities for fraudsters.
In an interview about open banking, Vax discusses:
What open banking means for institutions, customers and fraudsters; New vulnerabilities that arise because of open banking; How evolving regulatory mandates also influence cybersecurity response.Vax is a financial industry subject matter expert specializing in online application security and performance, with specific focus on digital banking fraud, digital identity-theft prevention, consumer information protection, and mobile banking security. With more than 17 years of experience in the security technology industry, Vax has held leadership positions for security product lines at Radware, Checkpoint Technologies and Compulite Industries. Vax received a Cum-laude MBA focused on strategy and entrepreneurship and was a leader for the Bomb Squad with the Israeli Defense Force handling explosive device inspection and explosive ordinance disposal.
A recently detected espionage campaign is delivered via malicious emails, but maintains presence on compromised machines by using scripts instead of a binary payload, Malwarebytes researchers have discovered.
The campaign was targeting a Saudi Arabia Government entity with emails containing a Word document weaponized with malicious macros. The scripts delivered using the macros were able achieve persistence on compromised systems and maintain communication with a command and control (C&C) server.
The attackers use scripts to fingerprint the victims’ machines and to deliver commands that are then executed via PowerShell. Communication with the server is made via hacked websites acting as proxies, Malwarebytes has discovered.
Featuring the logo of a Saudi Government branch, the malicious document, which also includes several Base64 encoded strings alongside the macro, prompts the victim to “Enable Content,” claiming it is in protected view.
The malicious VBScript first attempts to disable or lower security settings within Microsoft Excel and Word through altering corresponding registry keys. The script also fingerprints the victim for their IP address, and then proceeds to retrieve a stream of data from the Pastebin website using its own proxy.
The fetched data is converted into two scripts, one PowerShell and one Visual Basic. The latter is used for persistence via a Run key in the registry and a scheduled task and also acts as the launcher for the PowerShell script. Both are stored as hidden system files under the Documents folder.
The PowerShell script also carries instructions to lower the security settings for Microsoft Office, but its main function is to exfiltrate data and communicate with the C&C.
Data is exfiltrated via several hardcoded websites acting as a proxy.
The use of scripts as part of this campaign provides increased flexibility due to the modularity of the attack, in addition to ensuring increased stealth. While traditional malware can use a packer, this attack can’t, thus having to rely on various encoding techniques.
“This attack is very different from the typical malicious spam we see on a daily basis, blasting Locky or some banking Trojan. Indeed, there is no malicious binary payload (although one could be downloaded by the C&C) which makes us think the attackers are trying to keep a low profile and remain on the system while collecting information from their target,” the security researchers say.
Related: Rurktar Malware: An Espionage Tool in Development
Related: Iranian 'CopyKittens' Conduct Foreign Espionage
Windows Defender detection can be bypassed by tricking the antivirus application into scanning a different file or nothing at all, CyberArk Labs reveals.
The technique, which affects the scanning process over SMB shares, allows any malware to bypass Windows Defender and possibly other antivirus applications, researchers from CyberArk say.
Antivirus applications typically catch the execution of an executable file by a kernel callback and then scan the file, usually by requesting the user-mode agent to do so. The operation is different for executables already on the disk compared to those from a SMB share, the researchers explain.
If the executable file is already located on the hard drive, the antivirus won’t scan the process creation, because it scanned the file creation. However, the antivirus would scan the process creation when the executable is run directly from a SMB share, the security researchers explain.
One of the attack vectors involves tricking the antivirus into scanning a different file than the one actually executing. To ensure that one file is served to the Windows PE Loader and another to Windows Defender, a custom implemented SMB server is used.
Thus, when the process creation is made by Windows PE Loader and a request is made to the SMB server for the executable file, a malicious file is delivered. However, when Windows Defender requests the executed file, a benign file is served to ensure that the antivirus doesn’t stop the execution.
Thus, to abuse Windows Defender, an attacker would simply need to implement the SMB protocol and create a “pseudo-server” capable of differentiating between normal requests and those coming from Windows Defender.
One example, the researchers say, would be to decline the oplock request and return STATUS_OPLOCK_NOT_GRANTED, which would result in the scan failing and the malicious file being executed without interruptions. By blocking all handle creation requests with the impersonation level SEC_IDENTIFY one can also block the antivirus from scanning the file.
The attack is possible because the SMB protocol offers transparent integration into Windows, meaning that “accessing a remote file is performed like accessing a local file.” Thus, an attacker would need to create a handle to the file and then perform any operations using specific functions. However, replacing the file is possible for each operation, the researchers say.
CyberArk has contacted Microsoft to report the attack, but the company apparently doesn’t view the issue as a security vulnerability. In fact, the tech giant considers that the various special conditions required to trigger the bypass can be seen as a feature.
“Based on your report, successful attack requires a user to run/trust content from an untrusted SMB share backed by a custom server that can change its behavior depending on the access pattern. This doesn’t seem to be a security issue but a feature,” Microsoft reportedly told CyberArk.
Related: GhostHook Attack Can Bypass Windows 10's PatchGuard
Related: Old Kerberos Bypass Flaw Patched in Windows, Linux
Whole Foods Market, the supermarket chain acquired recently by Amazon for $13.7 billion, informed customers this week that it has launched an investigation after learning that some of its point-of-sale (PoS) systems may have been hacked.
The company has provided only few details as the investigation is ongoing. However, it said the incident appears to impact taprooms and full table-service restaurants located within some of its stores.
Whole Foods pointed out that these venues rely on different PoS systems than the store that houses them. The affected payment systems are also not connected to Amazon.com, the company said.
Law enforcement has been notified and a cyber security firm has been called in to assist Whole Foods’ investigation. The supermarket chain has promised to provide additional information as it learns more about the incident.
“While most Whole Foods Market stores do not have these taprooms and restaurants, Whole Foods Market encourages its customers to closely monitor their payment card statements and report any unauthorized charges to the issuing bank,” the company told customers.
The company’s statement suggests that it learned of the data breach from an external source – it’s likely that payment card issuers noticed a pattern of fraudulent transactions involving cards used at Whole Foods Market locations.
“Companies face threats every day and breaches will occur. In a contested environment like this, segmenting the networks, like Whole Foods did with its unique restaurant and taproom environment, saves other parts of the business from also being breached,” said Michael Daly, CTO of Raytheon's cybersecurity businesses.
“Financial systems within the larger Whole Foods system were not affected. The climate and operations controls were not compromised protecting massive amounts of food and inventory. Whether the segmented approach was happenstance or not, there is a lesson to be taken from today’s breach,” Daly added.
Fast food restaurant chain Sonic Drive-In is also investigating a possible data breach. Millions of payment cards that may have come from the company’s systems were recently put up for sale on a cybercrime marketplace.
Related: Kmart Payment Systems Infected With Malware
Related: Hundreds of Arby's Restaurants Hit by Card Breach
Related: Chipotle Investigating Payment Card Breach
Researchers claim Apple has silently patched a macOS vulnerability that can be exploited to bypass one of the operating system’s security features and execute arbitrary JavaScript code without restrictions.
The issue, discovered by Filippo Cavallarin of Italian security firm Segment, has been described as a local JavaScript quarantine bypass flaw and it has been assigned a risk rating of 3/5.
When a file is downloaded from the Internet, macOS places it in “quarantine” by assigning it the com.apple.quarantine extended attribute. This ensures that the user is alerted of the potential security risks before the file is executed.
Cavallarin said he found a way to bypass the file quarantine feature by exploiting DOM-based cross-site scripting (XSS) vulnerabilities in an HTML file named rhtmlPlayer.html, which is stored in the /System/Library/CoreServices folder of the OS.
According to the researcher, this file contains two DOM-based XSS vulnerabilities that can be exploited by hackers via Uniform Resource Identifier (URI) components.
One way to exploit the flaw is to use .webloc files, which allow users to save website addresses to the local system. On macOS, these types of files are automatically opened with the Safari web browser.
The attacker needs to embed the JavaScript code they want executed into a .webloc file, send it to the victim, and convince them to open it. Segment has published a detailed technical advisory and a video showing how an attacker can exploit this vulnerability to steal sensitive data from the targeted device:
The vulnerability is said to affect macOS 10.12, 10.11, 10.10 and likely prior versions of the operating system. The issue was reported to Apple via Beyond Security’s SecuriTeam Secure Disclosure (SSD) program and it was addressed without any mention in macOS High Sierra 10.13, which Apple released earlier this week.
Beyond Security told SecurityWeek that it informed Apple of the flaw on July 27. The company said the tech giant did not respond to its questions regarding the issue in the past two weeks.
SecurityWeek has reached out to Apple for clarifications and will update this article if the company responds.
This is not the only macOS vulnerability disclosed in recent days. Earlier this month, researcher Patrick Wardle demonstrated how unsigned apps can steal data from the Keychain password management system, and how attackers can bypass the Secure Kernel Extension Loading (SKEL) security feature.
Related: Apple Patches Hundreds of Vulnerabilities Across Product Lines
Related: Apple Patches Vulnerabilities Across All Platforms
Kaspersky said it had detected roughly 18,000 malware samples belonging to more than 2,500 families on industrial control systems (ICS) in the first half of 2017.
According to the company’s “Threat Landscape for Industrial Automation Systems” report for the first six months of the year, nearly 38 percent of the industrial systems protected globally by its products were targeted during this period. This is 1.6 percent less than in the second half of 2016.
Attempts to download malware or access malicious websites (e.g. phishing pages) were blocked by the company’s products on over 20 percent of the protected ICS devices.
Windows malware was neutralized on more than half of targeted systems. However, in many cases, attackers used scripting languages such as VBS, JavaScript, .NET, AutoCAD, Word macros and Java to implement malicious functionality.
Related: Learn More at SecurityWeek’s 2017 ICS Cyber Security Conference
“For computers that are part of industrial infrastructure, the Internet remains the main source of infection,” Kaspersky said in its report. “Contributing factors include interfaces between corporate and industrial networks, availability of limited Internet access from industrial networks, and connection of computers on industrial networks to the Internet via mobile phone operators’ networks (using mobile phones, USB modems and/or Wi-Fi routers with 3G/LTE support).”
The security firm, which last year launched a global computer emergency response team (CERT) focusing on ICS, noted that the number of attacks on these systems dropped in January, but returned to previous levels in the next months.
Kaspersky pointed out that many of the threats targeting ICS in the first half of 2017 were ransomware. The company’s products identified 33 different file-encrypting ransomware families on industrial automation systems.
Unsurprisingly, the highest percentage of attacks involved the notorious WannaCry ransomware, which leveraged NSA-linked exploits that can be triggered without user interaction.
Rockwell Automation, Schneider Electric, Honeywell, Siemens, ABB and other ICS providers published alerts at the time to warn customers about the possibility of being hit by WannaCry.

Related: Targeted Attacks on Industrial Sector Increasingly Common, Says Kaspersky
Related: Security Incidents Can Cost Industrial Firms $500K Per Year
Related: Industrial Companies Targeted by Nigerian Cybercriminals