Fraud News
Credential abuse attacks and identity theft incidents are rising, with attackers leveraging botnets to launch coordinated campaigns with high success rates, says Aseem Ahmed of Akamai Technologies, who shares best practices for mitigating the threats.
More than 30 billion malicious login attempts were carried out globally between November 2017 and June 2018, according to research conducted by Akamai, Ahmed says in an interview with Information Security Media Group.>
"The financial services industry is under constant attack from automated account takeover tools. ... E-commerce, travel and hospitality verticals are also very often targeted," he says.
It's difficult to determine the exact cost to the business from credential abuse attacks. Among the factors that must be considered, Ahmed says, are money lost, the cost of prevention and remediation, and customer abandonment rates after a credential abuse incident.
In this audio interview (see player link below image), which is the second in a two-part series, Ahmed talks about:
The cost to business from credential stuffing attacks; The industry verticals most impacted; Global best practices to mitigate credential abuse, including using a defense-in-depth approach.In part one of the interview, Ahmed discusses how malicious bots and botnets are becoming increasingly common and sophisticated and why enterprises need to address them in their risk assessments and security frameworks.
Ahmed is senior product manager for cloud security in Asia Pacific at Akamai Technologies. He is responsible for identifying market opportunities in cloud security, translating ideas into product requirements, gathering and consolidating customer feedback, evangelizing product vision and strategy, as well as overseeing aspects of the product design and development lifecycle while partnering with cross-functional teams on go-to-market activities. With over 10 years of experience in security services and consulting, cloud security solution architecture, incident handling and IT Infrastructure management, Ahmed has built a strong understanding of customer and market requirements. Previously, he has worked in technical roles at Microsoft and Convergys.
Cybersecurity , Endpoint Security , Fraud Management & Cybercrime
Top-Flight Information Security Conference Returns to London(euroinfosec) • December 4, 2018 Royal Dock Bridge on the southern side of the ExCeL conference center in London (Photo: Senseiich, via Wikimedia Commons)
Royal Dock Bridge on the southern side of the ExCeL conference center in London (Photo: Senseiich, via Wikimedia Commons)London is calling all information security professionals, as the Black Hat Europe conference returns to the U.K. capital for the third year in a row.
See Also: Live Webinar | Levers of Human Deception: The Science and Methodology Behind Social Engineering
The annual European conference, now in its 17th year, is being held this week at the ExCeL - short for Exhibition Center London - at London Docklands.
 ExCeL London (Photo: N Chadwick, via Creative Commons)
ExCeL London (Photo: N Chadwick, via Creative Commons)Organizers have booked 100 speakers and researchers who are again set to deliver 40 research-based briefings on Wednesday and Thursday. All of the briefings have been selected by the Black Hat Review Board, composed of 30 leading information security experts.
The diverse topics to be covered include politically motivated cyberattacks, recovering passwords from keyboards by using thermal emanations, hacking Microsoft Edge and detecting "deep fakes."
Where to begin? Here's my rundown of 14 especially good-looking briefings:
Day 1
Developments and Challenges in Cybersecurity from the Nation-State Perspective (Wednesday, 9:00): Marina Kaljurand, chair of the Global Commission on the Stability of Cyberspace, kicks off the conference with a keynote that will look back to 2007, when Estonia became the first country to be targeted by politically motivated cyberattacks. DeepPhish: Simulating Malicious AI (Wednesday, 11:45): Alejandro Correa Bahnsen of Cyxtera Technologies will offer tactics for identifying malicious TLS certificates in the wild, with a claimed accuracy of 95 percent. Attacking and Defending Blockchains: From Horror Stories to Secure Wallets (Wednesday, 14:00): Jean-Philippe Aumasson of Kudelski Security promises to review some of the most spectacular information security failures involving blockchain systems - bitcoin, ethereum and beyond - with an eye toward helping everyone involved to better mitigate their risks. Under the SEA - A Look at the Syrian Electronic Army's Mobile Tooling (Wednesday, 14:00): Mobile security firm Lookout's Kristin Del Rosso and Michael Flossman will offer a deep dive into the SEA's tactics, including its use of SilverHawk mobile surveillanceware. "To date, SilverHawk has been identified in over 30 trojanized versions of many well known apps, including Telegram, WhatsApp, Microsoft Word, YouTube, and the Guardian Project's Chat Secure app," they say. Video Killed the Text Star: OSINT Approach (Wednesday, 16:30): Francisco Gomez and Cesar Jimenez of Devo - the analytics and security firm, not the band - promise to round up machine learning techniques that can be used by open source intelligence analysts to determine if a preselected individual appears, or does not appear, in hundreds of hours of video. When Everyone's Dog is Named Fluffy: Abusing the Brand New Security Questions in Windows 10 to Gain Domain-Wide Persistence (Wednesday, 16:30): Magal Baz and Tom Sela Illusive Networks review how a Windows 10 security feature introduced in April can shred the safety of Windows domains and offer tools and techniques to help block attackers from using the security feature as a backdoor entrance into enterprises.Day 2
AI Gone Rogue: Exterminating Deep Fakes Before They Cause Menace (Thursday, 9:00): "Deep fake technology is an artificial-intelligence-based human-image blending method used in different ways such as to create revenge porn, fake celebrity pornographic videos or even in cyber propaganda," say Symantec's Vijay Thaware and Niranjan Agnihotri. They'll look at ways to combat deep fakes. Deep Impact: Recognizing Unknown Malicious Activities from Zero Knowledge (Thursday, 10:00): Researchers Hiroshi Suzuki and Hisao Nashiwa from Internet Initiative Japan discuss how tracking command-and-control servers as well as detecting exploit kits can help organizations to better spot malicious activity. The researchers say they're reliably able to track 14 different kinds of exploit kits, including Rig, Nebula, Terror, Sundown and KaiXin. Don't Eat Spaghetti with a Spoon - An Analysis of the Practical Value of Threat Intelligence (Thursday, 10:00): Can threat intelligence be used to predict malicious activity? Charl van der Walt and Sid Pillarisetty of SecureData have looked at whether malicious IP addresses, once detected, map to any ability to predict or track threats. Bleedingbit: Your APs Belong to Us (Thursday, 13:30): Researchers Ben Seri and Dor Zusman of Armis review Bleedingbit, which refers to two separate zero-day flaws in Bluetooth Low Energy chips used in Cisco, Meraki and Aruba wireless access points, that that an unauthenticated attacker could exploit to monitor all traffic flowing over the access point, inject malware and gain access to other parts of the network. Cutting Edge: Microsoft Browser Security - From People Who Owned It (Thursday, 14:45): With Windows 10, Microsoft jettisoned Internet Explorer for Microsoft Edge. But while heavily sandboxed, just how secure is Edge? Three researchers from Tencent Security Xuanwu Lab - Chuanda Ding, Zhipeng Huo and Wei Wei - who are veterans of the annual Pwn2Own hacking competition promise to describe logical sandbox escape attacks via three bugs in Microsoft Edge, only one of which has been publicly disclosed. These flaws "are entirely different from memory corruption bugs, as all we've done is abusing normal features implemented in the browser and operating system," the researchers say. The Mummy 2018 - Microsoft Accidentally Summons Back UglyAttacks from the Past (Thursday, 16:00): It's back to the future with security researcher Ran Menscher, who says that a reorganization of the Windows kernel reintroduced a flaw - CVE-2018-8493 - that attackers can use to intercept and modify packets as well as cause a denial of service. Thermanator and the Thermal Residue Attack (Thursday, 16:00): Three University of California at Irvine researchers - Tyler Kaczmarek, Ercan Ozturk and Gene Tsudik - offer "a framework for password harvesting from keyboard thermal emanations," which works on popular keyboards up to 60 seconds after a user has typed in their password. Black Hat Locknote (Thursday, 16:45): Bookending the opening keynote, the annual "locknote" features Black Hat founder Jeff Moss (@TheDarkTangent), joined by members of the Black Hat Review Board, discussing top issues facing the information security community.Beyond those sessions, another 30 briefings are also scheduled for the Business Hall, where vendors will be analyzing application security, infrastructure protection, identity and access management and more.
Black Hat Europe Arsenal, which allows researchers and the open-source community to deliver live demonstrations of tools they develop and use in their daily professions, also returns to the Business Hall. This year's arsenal will feature nearly 50 tools covering topics ranging from Android and iOS to mobile hacking and the internet of things.
Stay tuned for updates as I hit London this week for Black Hat Europe.
Secure multiparty computation technology enables users to carry out computation on private data while it remains encrypted, says Israel-based Yehuda Lindell, a cryptography professor who's chief scientist at the security firm Unbound Tech. One of the main applications is for protecting cryptographic keys, he says in an interview with Information Security Media Group.
SMC offers a more practical option to the usual practice of storing keys in a hardware security module, which is difficult to manage, he contends.
Using SMC, he says, "we can split the secrets into random pieces and put them on different machines and then have the computations being carried out without everything being bought together ... without the key being remembered," he says.
This new technology can be installed by deploying virtual machines to set up the framework, Lindell explains.
In this interview (see audio link below photo), he offers insights on;
Using SMC technology to protect cryptographic keys; The architectural framework required to carry out the computation for securing data. Potential other uses for SMC.Lindell, chief scientist at Unbound Tech, a cryptographic solutions provider, is a professor of computer science at Bar-Ilan University in Israel. He has published over 90 scientific articles and has authored one of the most widely used textbooks on cryptography and has years of industry experience in the application of cryptography to computer security.
Data Breach , Data Loss , Forensics
Answer: Yes, Q&A Site Believes Hackers Stole Private Content, Hashed Passwords(euroinfosec) • December 4, 2018
Next to corporate communications that claim that "your security is important to us," or that "protecting your information is our top priority," any post to a website titled "security update" means bad news.
See Also: Five Steps to Masterminding an Effective Security Awareness Program
So too for Quora. Following in the footsteps of numerous other breached businesses, the Mountain View, California-based question-and-answer site issued a data breach notification on Monday headlined "security update," by which it meant failure.
"We recently discovered that some user data was compromised as a result of unauthorized access to one of our systems by a malicious third party," Quora CEO Adam D'Angelo says in the breach notification, with "malicious third party" meaning hacker.
"We are working rapidly to investigate the situation further and take the appropriate steps to prevent such incidents in the future," he says, suggesting that it is belatedly paying for the information security practices, processes, technology and personnel that it should have already had in place, if it were to have prevented the breach in the first place.
Quora doesn't know how it was hacked. "We're still investigating the precise causes, and in addition to the work being conducted by our internal security teams, we have retained a leading digital forensics and security firm to assist us," D'Angelo says. "We have also notified law enforcement officials."
Exposed: Private Content
Quora says it believes that about 100 million users were affected by the breach.
Question: How many users does Quora have?
Answer: As of September, about 300 million active monthly users.
Quora says the attacker appears to have stolen:
Account information: Name, email address, "encrypted (hashed) password," as well as "data imported from linked networks when authorized by users." Public content and actions: "Questions, answers, comments, updates." Private content and actions: Answer requests, "downvotes," as well as any direct messages users might have sent.Reset Passwords
Quora says all users will have to change their passwords, which is a best practice for any user of any site that's been breached.
"Out of an abundance of caution, we are logging out all Quora users who may have been affected, and, if they use a password as their authentication method, we are invalidating their passwords," the company says in its data breach notification (see: Experts' View: Avoid Social Networks' Single Sign-On).
It goes without saying that everyone, at all times and with no exceptions, should never, ever use the same password on more than one site. Doing so makes it child's play for attackers to launch credential-stuffing attacks. These involve taking an email address and password pair obtained from a data breach or leak - for example, from Quora - and plugging it into a number of other sites and services, to see where else it might work (see: Credential Stuffing Attacks: How to Combat Reused Passwords).
Pandemonium, identity theft and fraud may follow.
In short: Use a password manager to generate and store strong, unique passwords for every site and service you use, or suffer even worse consequences than having your private questions and answers get exposed in a data breach.
Follows Marriott Breach Alert
On Friday, hotel giant Marriott disclosed that a hack that apparently began four years ago with its Starwood-branded hotels, which it purchased in September 2016, persisted until Sept. 10. So far, Marriott believes that up to 500 million individuals' personal details were exposed (see: Marriott Mega-Breach: Will GDPR Apply?).
Unlike Quora, however, Marriott appears to have tried to bury its bad news by releasing it on a Friday. That's a well-worn public relations strategy - beloved by businesses and politicians alike - for trying to minimize news coverage and capitalize on the fact that fewer people may be following news outlets on Saturday (see: Chipotle: Hackers Dined Out on Most Restaurants).
Breach Response , Data Breach , Data Loss
Legal Experts Suspect So, But Investigation Could Take a Year or More(euroinfosec) • December 3, 2018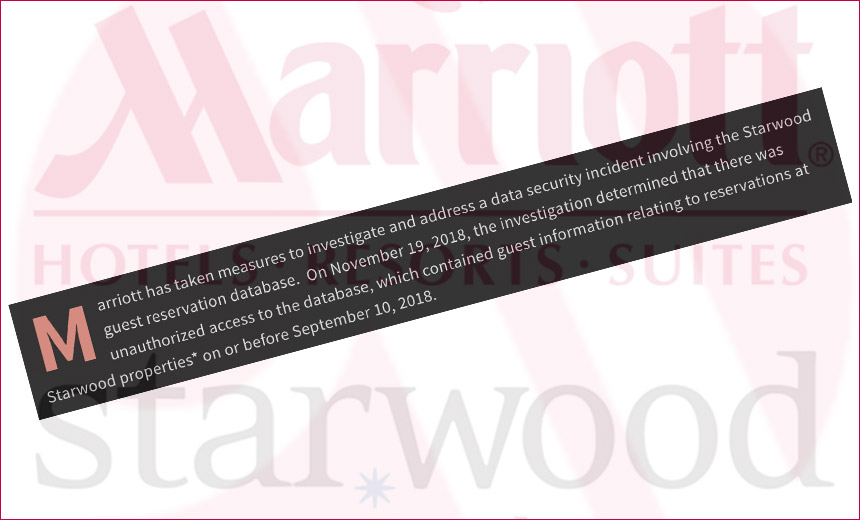
Will Marriott be the first organization to feel the full force of the EU's General Protection Regulation potential penalties over a breach that appears to have exposed up to 500 million individuals' personal details?
See Also: Third-Party Cyber Risk Management - A Data-Driven Approach
Since May 25, when GDPR went into full effect, privacy watchers have been wondering if any newly discovered breaches - British Airways, Cathay Pacific, Dixons Carphone - involving Europeans' personal data might lead to a breached business being the first to feel EU privacy regulators' full fury.
What's unclear, however, is how privacy regulators might impose sanctions for breaches that began before GDPR came into effect, but which persisted after May 25.
Legal and privacy experts, however, have told me that regulators have been clearly signaling that any breach that spans May 25 will fall under GDPR's purview.
Marriott's Mega-Breach
In an era of mega-breaches, Marriott stands out as being more "mega" than many. But like so many breaches of any size, it appears to trace to a simple-sounding cause: unauthorized database access.
 Marriott believes that its Starwood database breach exposed information on 327 million individuals worldwide. For comparison, here's a list of the previously biggest known data breaches in history. (Source: Have I Been Pwned)
Marriott believes that its Starwood database breach exposed information on 327 million individuals worldwide. For comparison, here's a list of the previously biggest known data breaches in history. (Source: Have I Been Pwned)On Friday, Marriott first disclosed that it had discovered signs of an intrusion in its guest reservation network on Sept. 8, affecting numerous properties worldwide. On Nov. 19, it confirmed that attackers appeared to have encrypted and copied data for many of the victims that included including names, mailing addresses, phone numbers, email addresses, passport numbers, and, in some cases, encrypted payment card information.
Marriott says the breach appears to have begun with a 2014 network hack of Starwood Hotels & Resorts Worldwide, which Marriott acquired in September 2016 for $13 billion (see Marriott's Mega-Breach: Many Concerns, But Few Answers).
Meanwhile, attackers' access may have persisted for four years, obtaining customer data pertaining to reservations at various properties until "on or before Sept. 10, 2018," Marriott says in its breach notification.
Bonus question: What do Aloft, Design Hotels, Element, Four Points by Sheraton, Le Méridien, Sheraton, St. Regis, The Luxury Collection, Tribute Portfolio, W Hotels and Westin have in common?
Marriott has said that hackers accessed its "Starwood guest reservation database," and those 11 types of properties are part of Marriott's Starwood brand.
History Lesson
Expect Marriott to try to spin this breach as being a historical incident that spiraled out of control.
"There is a paradox now where it is in a company's interests to emphasize the historic nature of a data security incident and state how long an incident has been running and how long systems have been exposed to seek to show that the GDPR should not apply," Ian Birdsey, a partner at Pinsent Masons who specializes in cyber risk, says in a blog post. "This reflects the size of the potential financial penalties that can be levied under the GDPR when compared to pre-GDPR legislation."
Taking the U.K. as an example, before GDPR came into effect, the Data Protection Act 1998 applied. When privacy regulators found that companies had violated the DPA - due to poor security practices, for example - they could impose fines of up to £500,000 ($640,000). Only two organizations - Equifax and Facebook - received the maximum penalty.
But organizations that violate GDPR face fines of up to 4 percent of their annual global revenue or €20 million ($22.7 million) - whichever is greater - as well as other potential sanctions, including losing their ability to process personal data. Separately, organizations that fail to comply with GDPR's reporting requirements also face fines of up to €10 million ($11.3 million) or 2 percent of annual global revenue.
The U.K.'s privacy watchdog, the Information Commissioner's Office, says GDPR penalties - as enacted in the U.K. via the Data Protection Act 2018 - are not meant to be punitive. Organizations that try to do the right thing won't be punished simply for failing. Also, the 72-hour deadline for an organization to alert authorities in the case of some types of breaches isn't meant to serve as a "gotcha," but rather so that regulators can help (see: GDPR: UK Privacy Regulator Open to Self-Certification).
You Buy It, You Own It
Marriott wouldn't be the first organization to have been hacked due to systems it acquired and then failed to properly manage or secure. But it should not count on this to assist its data security defense.
Take TalkTalk, which was hacked in 2015 via SQL injection attacks against a database that was originally created by Italian telecommunications firm Tiscali.
An ICO investigation found that after TalkTalk acquired Tiscali's U.K. operations in 2009, it failed to properly catalog and manage the acquired infrastructure. Fast-forward to 2015, when hackers used an automated vulnerability scanning tool to exploit a SQL injection flaw in a MySQL open source SQL database management system. Again, it had been created by Tiscali, but was then owned by TalkTalk, which had failed to apply a 2012 patch to the database that would have eliminated the critical MySQL flaw exploited by attackers.
After a year-long investigation, the ICO slammed TalkTalk with a fine of £400,000 ($515,000), which was a record at the time (see: Two Friends Who Hacked TalkTalk Receive Prison Sentences).
Countdown to Late 2019
As privacy watchers wait to see whether EU data protection authorities apply GDPR to the Marriott breach, one thing is clear: We likely won't know one way or another for some time.
For starters, that's because Marriott is still investigating the breach. As such investigations progress, breached businesses may find that the intrusion is better or worse than they initially suspected (see: Data Breach Notifications: What's Optimal Timing?).
In the aftermath of really big breaches, organizations often appear before the U.S. Congress, U.K. Parliament, European Parliament or other legislative bodies to answer pointed questions, leading to further details coming to light.
As has been seen in past DPA investigations conducted by the ICO and the Dutch Autoriteit Persoonsgegevens, major probes into Equifax, TalkTalk and Uber may take a year or more to conclude.
So when it comes to seeing how Marriott's Starwood breach plays out on the regulatory front, stay tuned for 2019, or maybe even beyond.

